
Reduce your time to detection and protect your business in real time.
Vulnerability management, as part of an organization’s security strategy, is critical so you can identify, correct, and report on the threats to your business systems and networks. 11:11 Continuous Risk Scanning provides deep, contextual risk analysis to prioritize vulnerabilities and minimize an organization’s “attack surface.”
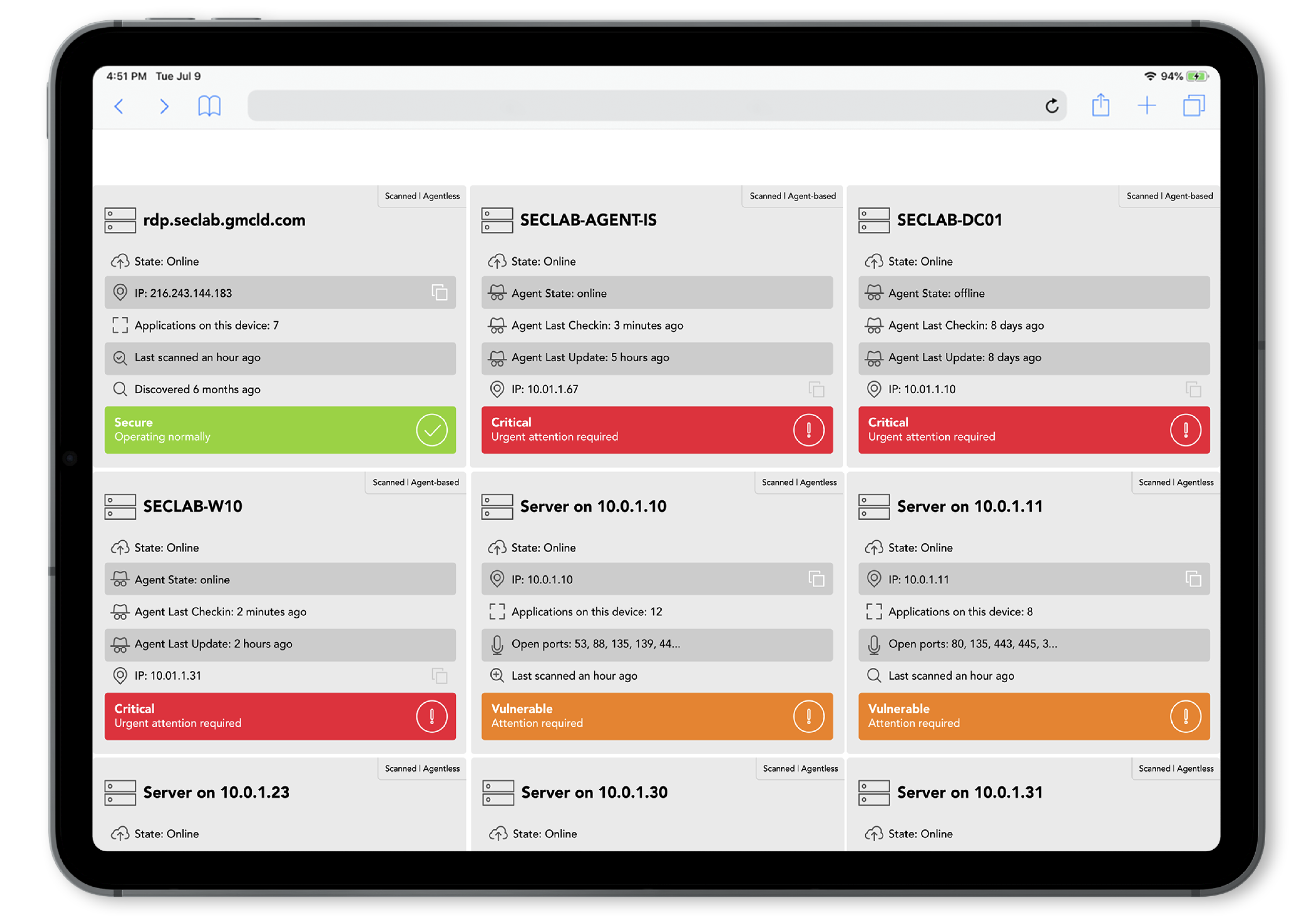
With Continuous Risk Scanning you quickly and easily gain visibility into all your assets, allowing you to create a vulnerability management program based on your unique needs. Get a complete assessment of the vulnerabilities to your business and ongoing analysis of threats so you can respond quickly.
Product Features
11:11 Continuous Risk Scanning includes:
Baseline Analysis
Our contextual risk scoring engine employs machine learning to analyze your network based on more than 30 vulnerability metrics. This provides an accurate score of the most relevant risks to your organization, including:
- Most common vulnerabilities
- Authentication/Authorization issues
- Missing data encryption
- OS command and SQL injection
- Software bugs
- Weak passwords
- Missing integrity checks
- URL redirection
- Site trust issues
Comprehensive Reporting
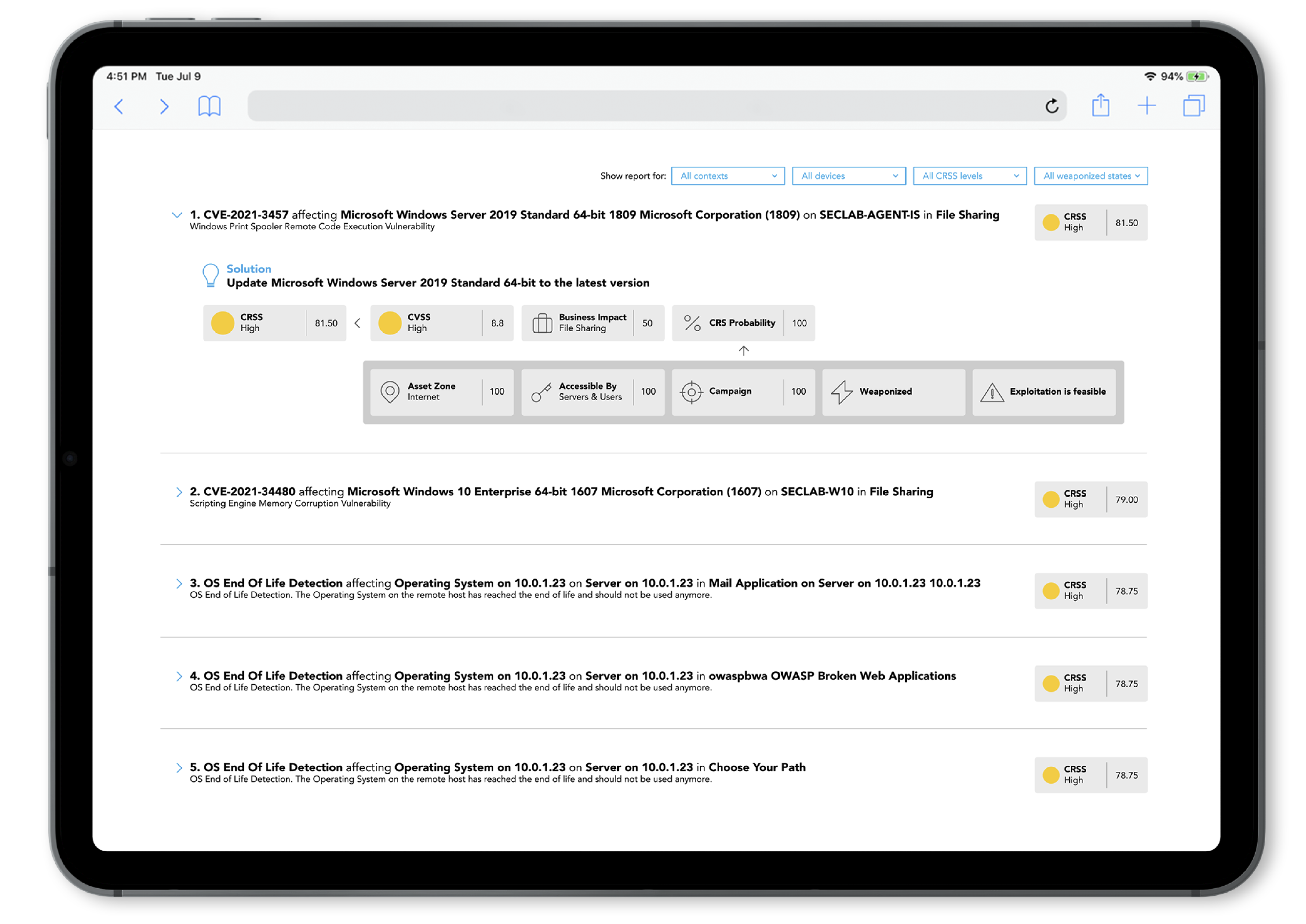
Once all assets have been identified, Continuous Risk Scanning provides you with deep and accurate reports into the threats that pose the greatest risk to your business:
- Vulnerability Reports deliver snapshots or historical vulnerability assessments of your environment, as well as risk metrics for your IT team and senior management to review.
- Contextual Risk Scoring Reports focus on the most critical vulnerabilities, particularly noting any threats with potential to be exploited.
All reports can be filtered and exported.
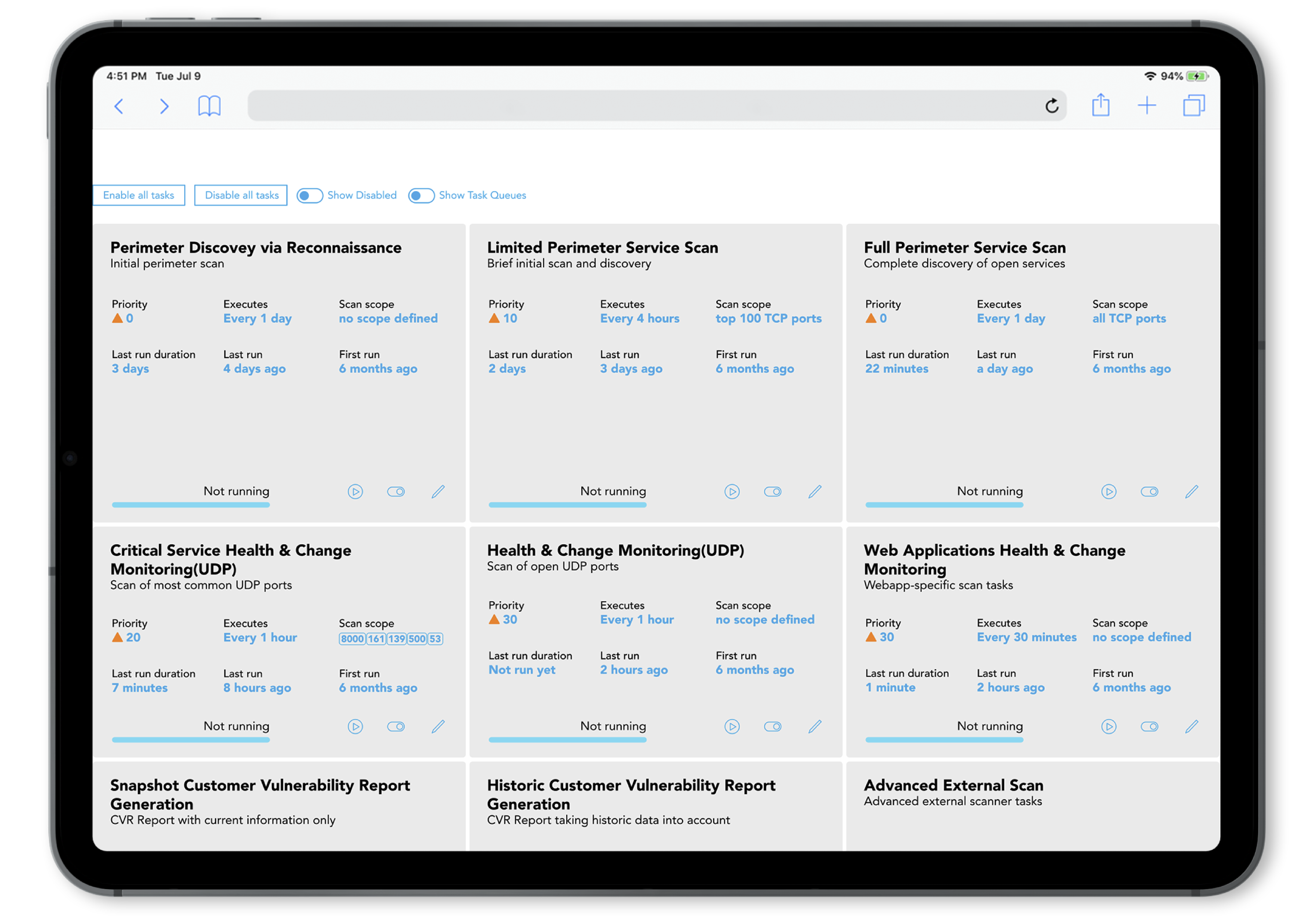
Continuous Scanning
After the initial vulnerability analysis and reporting, Continuous Risk Scanning automatically and continually runs assessments of your network based on a predefined schedule. When it detects any change in the environment, it quickly updates Vulnerability Reports so you’re always getting the most up-to-date vulnerability management information.
Continuous Risk Scanning Benefits
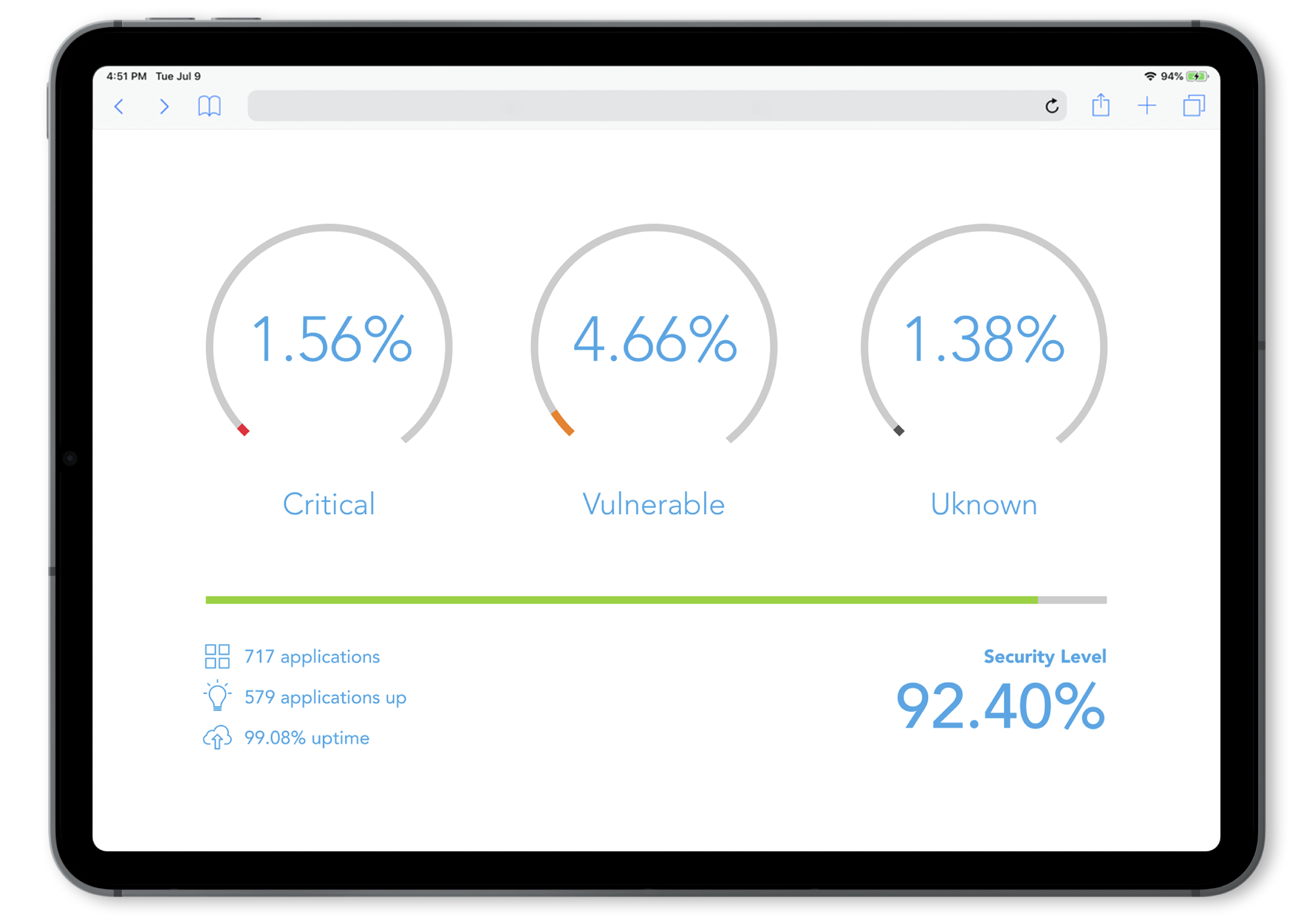
The complete picture.
Get a high-level view of your environment, and understand how vulnerabilities could impact your critical assets.
Deep analysis.
Identify vulnerabilities that lie deep within your environment that is much more comprehensive than analysis available with other scanning tools.
Prioritize specific alerts.
Not all assets are equal in terms of business value. Continuous Risk Scanning gives you the ability to “reduce the noise” and focus on what matters most.
Available in all geographies that 11:11 Systems operates.
Designed to meet your unique, global business requirements.
11:11 Systems’ data centers meet the highest standards for security, compliance, and performance. With global availability, consistent infrastructure design, and unparalleled scale and flexibility, our cloud regions will be ready to support your changing business needs.
FAQ
Continuous Risk Scanning can be used to perform both credentialed and non-credentialed scans using agent-based scanning or agentless scanning with an appliance installed in the network.
11:11 CRS is priced on a per-IP model.
Yes. The current minimum is 30 IPs.
Yes. We can scan up to 22 subnets in a single targeted scan.
